Some people still don’t know, but it’s not common for identity theft to begin with dramatic breaches or obvious account takeovers. Actually, most incidents originate from minor data exposures that go unnoticed for months before financial or legal damage surfaces. Things like reused passwords or a forgotten online subscription can expand your digital footprint until it becomes vulnerable to exploitation.
That’s why understanding how identity theft develops lets you treat prevention as a monitoring process and not like a reactive cleanup effort after fraud occurs. In this guide, Insiderbits explains how personal data can be exposed, which access points attackers exploit most frequently, and how monitoring apps can function as an early-warning radar that restores control over your digital identity.
- 5 Best Personal Safety Apps For Peace of Mind
- AI Personal Assistant App
- AI Personal Stylists: Redefining Fashion Choices
How personal data gets exposed without any warning
Personal data exposure almost never happens in a single event. Usually, most identity theft cases begin with small pieces of information distributed across dozens of digital platforms.
For example, a phone number linked to a delivery may appear insignificant in isolation, yet each data point expands the digital footprint that surrounds an individual.
When one of these platforms experiences a security breach, even limited information can be extracted and later combined with data obtained from other incidents.
Then, criminal networks aggregate fragmented records from multiple leaks to reconstruct a more detailed identity profile.
In addition, exposure increases through data broker ecosystems that collect and resell consumer information for marketing purposes.
Or old accounts that were never deactivated or credentials reused across services further widen the surface area.
The progression is incremental and typically invisible, which is why many individuals discover the problem only after fraudulent credit activity occurs.
Therefore, identity protection is a continuous measure and helps reduce the likelihood that silent data accumulation evolves into financial or reputational damage.
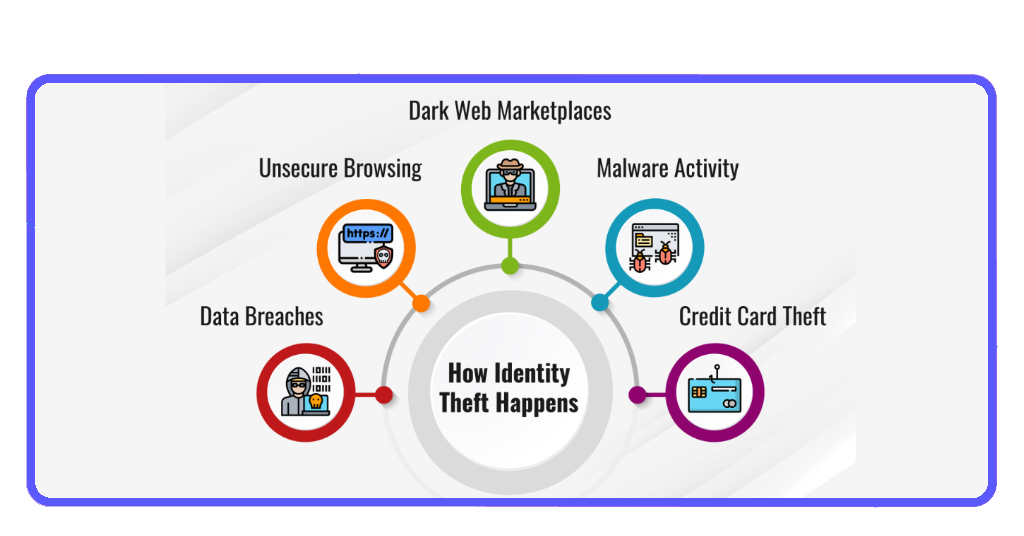

The most common entry points hackers exploit
Attackers frequently target login credentials reused across multiple websites, since one compromised password can unlock access to banking, social media, retail, or email.
Phishing emails also remain a dominant entry method, tricking users into voluntarily submitting verification codes or account details.
That said, social engineering tactics exploit publicly available information to impersonate legitimate institutions.
Meanwhile, unsecured Wi-Fi networks may expose session data to interception.
Each of these entry points relies on small lapses in digital hygiene rather than sophisticated technical intrusion.
If you notice these patterns, you can shift the focus from fear to awareness, reinforcing the importance of checking account security settings and authentication methods regularly.
Identity theft risks you should check right now
Identity theft risk never announces itself with an obvious alert.
It usually comes from unfamiliar login notifications, unexpected password reset emails, unexplained charges, or inquiries from lenders you never contacted.
Those are some of the examples that may signal that personal data is circulating beyond your control.
It also indicates that fragments of your identity could already be exposed, even if no direct financial loss has occurred yet.
Thankfully, there are automated identity monitoring platforms that function as preventive radars. Check below for two platforms Insiderbits is highlighting:
Aura Security
Aura Security is an identity protection platform that scans for exposed credentials and evaluates potential fraud signals across financial and online environments.
The platform typically monitors dark web marketplaces and other records to detect anomalies associated with your identity profile.
When suspicious activity is identified, users receive alerts that let them take safety measures before further escalation.
LifeLock
On the other hand, LifeLock emphasizes credit monitoring, fraud detection alerts, and identity restoration support designed to assist users if misuse occurs.
The service monitors credit bureau data and certain transactional indicators for irregular activity that may signal unauthorized account openings or fraudulent financial behavior.
When alerts are triggered, the system guides users through next steps such as fraud alerts or credit freezes.
See which accounts and details are most vulnerable
Aura Security and LifeLock are two digital monitoring platforms that provide visibility into potential exposures by scanning for leaked credentials.
Both platforms typically monitor credit activity, data breach reports, and certain public databases to identify anomalies associated with your identity profile.
With that, alerts are delivered through mobile notifications or dashboard summaries, granting a chance for users to respond before fraudulent use expands.
Viewing monitoring tools as preventive radars, rather than panic-driven solutions, reinforces autonomy and informed decision-making.
Lock down your information before damage happens
When it comes to reducing identity theft exposure, the process begins with enhancing authentication protocols, including passwords and multifactor verification across accounts.
That includes regular password updates and secure storage tools that limit the impact of isolated breaches.
Also, remember to remove outdated accounts, and limit personal data sharing on public platforms to further decrease surface exposure.
Lastly, it’s also a good idea to have consistent credit monitoring and rapid response to suspicious alerts, which helps contain potential damage early.
Identity protection is ultimately a process of continuous awareness supported by structured monitoring tools and disciplined digital habits.
Taking preventive steps today strengthens long-term control over your financial and personal information.
Identity theft: check how exposed your personal info really is – Conclusion
Identity theft develops gradually, often from overlooked exposures that accumulate across digital platforms over time.
Treating prevention as an ongoing audit process brings awareness and reduces vulnerability before financial harm occurs.
With monitoring tools, you form a layered defense that restores control to the individual. Acting early limits escalation and preserves both financial stability and personal reputation.
Related: Easy step-by-step guide to recover your Google Account easily
Enjoyed this article? Save Insiderbits to your favorites and discover the most useful tech tips!